
SMS phishing - also known as smishing - is, as the name suggests, a variation of classic phishing that relies on SMS messages instead of classic e-mail.
The reasons behind the use and increasing popularity of smishing attacks are various.
First, there is a psychological factor based on a general trust in SMS messages. The majority of people are now quite aware of the dangers of spam- and Phishing emails consciously and often takes a critical look at unknown e-mails.
Our mobile phones and smartphones, on the other hand, are private devices that we generally trust more. Ignorance of such dangers plays an enormous role here.
For these and other reasons, such as the general flood of spam e-mails, only about 20% of all e-mails are read and only 3% are answered. With SMS messages, however, the situation is completely different: Here, a total of 98% of all messages are read and 45% are also answered.
The chances for criminals that their scam messages will be noticed is significantly higher than with classic phishing. In addition to the psychological factor, there is also the technical side as a clear success factor. Smartphones are simply often much less well protected than e.g. B. Computers in workplaces and thus more prone to dangerous Malware.
Just like classic phishing, smishing also has clear goals for the perpetrators. These coincide with those of classic phishing and can generally be divided into three major areas:
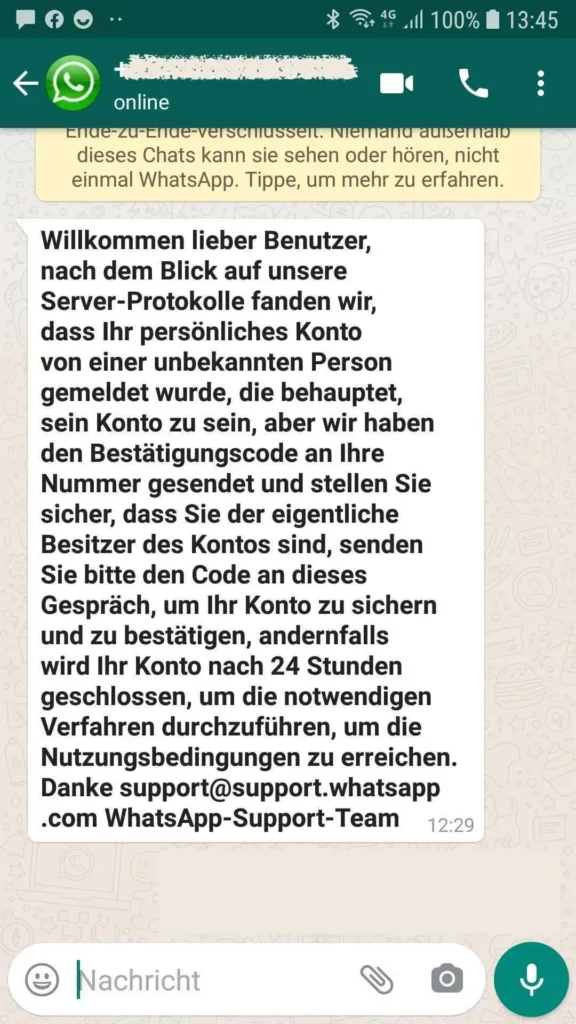
Smishing attacks often aim to steal login data for online accounts. The login information for online banking is traditionally particularly popular with criminal hackers. They even benefit from messages from the "real" banks, which often send warnings in the form of an SMS notification if there is unusual account activity.
This form of smishing is so popular that it even got its own name - "bank smishing". Here, too, the possibilities of modern technology are often underestimated: For example, it is possible to disguise or forge the sender of an SMS. Messages are sent from a computer and then automatically assigned to a legitimate sender number on the victim's smartphone. So, never share your account information. They are private and nobody's business. There's no reason a reputable company would ask for login credentials from your customers.
Getting the victim to download an infected file is the classic goal of phishing, but it's also not unknown in smishing, although it's used less frequently. An incident in the Czech Republic showed that the method can still be promising. Thousands of people were tricked into installing an app – allegedly from the Czech Post – via SMS. This was a Trojan that compromised not only credit card information but also other app accesses.
Overall, the spread of malware in smishing attacks is less frequent, since the smartphone developers have now reacted and are making it increasingly difficult to install unsigned or unverified apps. The danger remains, especially with Android devices, there is the so-called "app sideloading", where apps from unknown sources can be loaded if this is not deactivated in the device settings (this feature is deactivated by default).
With the development and spread of so-called VoIP telephony and caller IDs, fraudsters and cybercriminals have also come across new techniques to reach victims via a fake number. With "Call ID Spoofing", the caller's actual number, the so-called "Network Provided Number", is replaced with a false number. There are countless dubious providers who offer their customers the option of changing the network provided number themselves. However, this is not to be confused with "CLIP No Screening", an actual service feature in which the outgoing number, the so-called "User Provided Number", can be freely selected, but only on the condition that the rights to the number owns.
Forging and masking SMS senders is therefore not a major technical hurdle either. Here, too, there are free providers on the market who not only let you choose the sender number, but even a name. SMS notifications with names such as "Papa" or "Mama" or even "Police" are not uncommon. This is possible, among other things, because the field that shows us the transmitted number is completely separate from the actually registered number.
Many dangers lurking on the Internet require active protection. For example, the risk of Trojans and viruses is reduced with the active protection of a virus scanner. With smishing, on the other hand, active protection is not necessary to protect yourself. It is often enough to do nothing. Phishing in general only becomes a threat if the victim falls for the scam. Not reacting to the attempt at all protects. However, there are a few things you can do to increase your awareness of the dangers of smishing:
