CI/CD systems automate build and release processes. If they are compromised, attackers can officially release manipulated code – with all the necessary credentials.
Supply chain attacks on open-source packages are no longer an isolated developer problem. The recent "Mini Shai-Hulud" incident dramatically illustrates just how vulnerable digital value chains have become – even when modern security mechanisms like signed build processes or SLSA attestation appear to be working. For CEOs, CIOs, CISOs, and CSOs, one thing is clear: this isn't about code quality, but about business risk, industrial espionage, and potentially existential liability issues. Anyone using open source – and what company doesn't? – is part of a global risk architecture that is currently being systematically exploited.
The current campaign surrounding the "Mini Shai-Hulud" worm affected prominent projects in the npm and PyPI ecosystems – including TanStack, Mistral AI, Guardrails AI, UiPath, and OpenSearch. Dozens of packages and numerous versions were affected. The compromise was attributed, among other things, to the vulnerability... CVE-2026-45321 Assigned with a CVSS score of 9.6 (critical). Details on the assessment of critical vulnerabilities are documented in the NIST National Vulnerability Database (NVD).
What makes this case strategically significant is that the manipulated packages were released via regular release pipelines and carried valid SLSA Level 3 attestations. Information on Secure Supply Chain SLSA framework are documented on the official project website.
This called into question a central assumption of many security strategies: that formally secured build processes automatically imply trust.
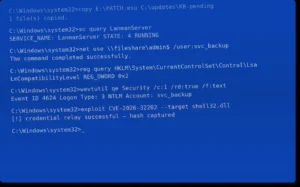
The attackers exploited a chain of vulnerabilities within GitHub Actions. Specifically, they combined mechanisms such as "pull_request_target", cache poisoning, and the extraction of OIDC tokens. The underlying principle is easy to explain:
The result: malware that looks like officially released code.
The MITRE ATT & CK The framework describes comparable techniques involving privileged token use and supply chain manipulation.
The worm continued its spread: It actively searched for npm tokens with the "bypass_2FA" option enabled. Once such a token was found, the worm infected all further packages from that maintainer, creating a self-propagating supply chain infection.
Simultaneously, the malware installed monitoring mechanisms for GitHub tokens, manipulated CI/CD workflows, and exfiltrated repository secrets to external servers. The data leaks occurred via decentralized messaging infrastructures such as Session Protocol – a deliberate attempt to circumvent traditional corporate blacklist mechanisms.
For companies, this means:
CISA has been warning about this for years Software supply chain risks and has published corresponding guidelines.
The economic damage from traditional cyberattacks is measurable. Supply chain attacks, however, have a systemic impact. They don't just affect one company, but entire ecosystems. And they undermine trust – the most important currency of digital business models.
Particularly alarming is the fact that the manipulated packages carried valid security credentials. This marks a paradigm shift: trust is no longer built on "formal security," but on continuous validation.
Or to put it another way: Compliance is not the same as resilience.
The OWASP The software supply chain now has its own guidelines and best practices, which emphasize the need for deeper security architectures.
For company management, three key questions arise:
Supply chain attacks are not an IT problem – they are a board issue.
The malware used targeted not only cloud access and crypto wallets, but explicitly CI systems and AI toolchains. This suggests strategic goals: intellectual property, training data, proprietary models, and business logic.
Those who gain access to build pipelines and secrets can:
This is digital industrial espionage on a new level.
Simply applying patches is not enough. A structural reorganization is necessary.
Zero Trust principle also in the developer ecosystem
Not only create SBOMs, but also monitor them.
A Software Bill of Materials (SBOM) is only valuable if it is actively monitored – including transitive dependencies.
Continuous pipeline validation
Static code scans are not enough. What's needed is:
Executive Reporting
Supply chain risks belong in Enterprise Risk Management (ERM) and in board communications.
The misconception that "Open Source is a community matter""
Many companies delegate open-source responsibility to development teams. This is negligent.
Open source is part of your product architecture. Therefore, it is part of your company valuation.
Investors, regulators and customers are increasingly asking for:
Companies that cannot present a clear strategy here risk competitive disadvantages.
Large corporations have dedicated security teams. Mid-sized technology companies, on the other hand, often rely on standard GitHub workflows without in-depth auditing. It is precisely in these cases that infected dependencies can remain undetected for months.
The risk is not theoretical. A single compromised packet in the backend can expose customer data, IP addresses, and cloud access credentials.
The Mini-Shai-Hulud case shows that even valid medical certificates do not offer absolute security. Security must be considered dynamically.
Businesses need:
The goal is not to avoid open source – but to use it in a controlled manner and with structural protection.
ProSec helps companies to strategically secure their digital supply chain – not in isolated instances, but systemically.
Our services include:
We combine in-depth technical analysis with economic risk assessment. Because in the end, it's not about code – it's about business resilience.
A supply chain attack does not target a company directly, but rather its supply chain – for example, software libraries, service providers, or cloud providers. The actual attack then takes place via these "trusted" components.
SLSA (Supply-chain Levels for Software Artifacts) is a security framework for securing software build and release processes. It defines maturity levels for trust credentials in the software supply chain.
An OIDC (OpenID Connect) token is a short-lived authentication credential used in modern cloud and CI systems to securely exchange identities between services.
A software bill of materials is a structured list of all components contained in a software program. It serves to create transparency regarding dependencies and potential vulnerabilities.
CI/CD systems automate build and release processes. If they are compromised, attackers can officially release manipulated code – with all the necessary credentials.
We use cookies, and Google reCAPTCHA, which loads Google Fonts and communicates with Google servers. By continuing to use our website, you agree to the use of cookies and our privacy policy.