The Chrome DevTools protocol allows monitoring of internal network traffic and processes within the Chrome browser. Malware can exploit this protocol to intercept network data or manipulate content.
The threat from cyberspace is changing silently and rapidly. While many companies focus their resources on phishing, DDoS attacks, or well-known ransomware campaigns, new attack vectors are emerging under the radar of IT security departments – sometimes with devastating consequences.
A recent incident uncovered by Palo Alto Networks exemplifies how seemingly distant platforms like Discord can pose concrete risks to corporate networks. The discovery of a new type of info-stealing malware called "VVS Stealer," targeting Discord and browser data, is not an isolated case. Rather, it is a symptom of a growing cyber economy where automation, obfuscation, and deception have long since left the domain of script kiddies and are now being operated by organized groups.
The complexity of the attacks is less important than the ease with which they can be scaled and distributed – often via publicly accessible channels like Telegram. Companies are no longer just targeted as potential victims. Far more dangerous is the fact that they become unwitting accomplices in a criminal infrastructure.
What does this mean specifically for you as CEO, CIO, CISO or CSO – and how can you protect your company, your brand and your supply chain from it?
VVS Stealer is a Python-based information thief that specifically targets Discord users. The malware is available on Telegram for as little as €10 per week. This alone is alarming: it makes VVS one of the cheapest stealers on the market – and therefore easily accessible to a broad range of attackers. Its modular nature (various license packages from one month to lifetime) and the use of legitimate tools like Pyarmor for obfuscation make the malware attractive to less technically savvy but highly motivated groups.
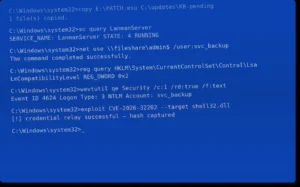
The attack chain begins with distribution via obfuscated EXE files (packaged using PyInstaller) and ends in a system that opens new entry points for the attacker with every reboot. The malware ensures its own persistence by adding entries to the Windows operating system's startup programs. Once active, it begins stealing valuable information, including:
A particularly insidious feature is one that hijacks active Discord app sessions. To achieve this, VVS Stealer uses a technique called injection: First, Discord is shut down, and then a manipulated JavaScript file is downloaded from the web. This file then spies on the app's network traffic via the Chrome DevTools Protocol.
The result: An ongoing session can be manipulated, exploited, and taken over – the attacker literally assumes the user's digital identity. If Discord is used for internal communication, community management, or developer access, for example, this creates a significant risk of data leaks or impersonation attacks.
A particularly worrying aspect of this threat is that victim organizations are themselves being turned into Malware distributors – without realizing it.
Who security researcher Hudson Rock reports that cybercriminals are using stolen administrator credentials from companies to exploit their web servers and domains to spread malware. This form of misuse of company infrastructure—for example, via compromised FTP, CMS, or SFTP access—is not only detrimental to data integrity. It also destroys brand trust among partners, customers, and search engines.
This creates a vicious cycle for companies: First, login credentials are stolen, then their own IT becomes the entry point for malware that scales the same methods. The malware is no longer spread solely via criminal command-and-control servers, but also via domains that are actually trusted – a prime example of supply chain risks in the digital context.
Traditional security mechanisms are reaching their limits in this threat landscape. Using Pyarmor as an obfuscation tool allows the source code of Python scripts to be obfuscated in such a way that common antivirus programs or signature-based scanners are largely ineffective.
Furthermore, there's the "low and slow" tactic: By minimizing system resource usage and using simple dialog boxes (e.g., "Fatal Error – Please restart your PC"), VVS remains inconspicuous. The user believes it's a temporary system problem – in reality, the attack has already begun.
These attack mechanisms are not purely technical in nature. Their core elements lie in deception, process exploitation, and a lack of control over shadow infrastructures. For you as a business decision-maker, this is therefore not about isolated technical fixes – but about strategic control mechanisms on four levels:
While many security providers focus on technological patching or tool-centric endpoint solutions, ProSec takes a holistic approach: As experts in technical information security, economic crime investigation and counter-industrial espionage, we understand the multifaceted threat landscape better than anyone else.
We help companies – from medium-sized businesses to large corporations – with the following specific measures:
Our Red Team methodology combines realistic attacker strategies with legal procedures – this allows us to discover vulnerabilities before perpetrators exploit them.
And: As an independent partner, we represent exclusively your interests – not those of a tool manufacturer.
Anyone who still believes that external communication or chat platforms like Discord are merely "private playgrounds" for employees is overlooking the growing interconnectedness of private and professional IT spheres. Information theft – even in the form of simple €10 subscriptions – is becoming an organizational threat, holding companies hostage between loss of control and breach of trust.
The faster leaders recognize this shift in reality and incorporate it into their security architecture, the less damage and the higher the resilience in the digital space.
ProSec is at your side as a committed, methodologically sound and experienced partner.
Infostealers are malicious programs designed to steal information such as passwords, login data, cookies, or autofill data from infected systems – usually unnoticed in the background.
Obfuscation refers to the deliberate concealment of code, for example to make analysis more difficult. This protects the malware from detection by signature-based antivirus programs and reverse engineering.
Discord injection involves injecting active code into the processes of the Discord app to modify or take over the current session. The goal is to gain control over the user's account.
Shadow IT encompasses all IT systems, applications, or services that are used in a company without the knowledge and approval of the IT department – e.g., private cloud storage or messenger installations.
The Chrome DevTools protocol allows monitoring of internal network traffic and processes within the Chrome browser. Malware can exploit this protocol to intercept network data or manipulate content.
We use cookies, and Google reCAPTCHA, which loads Google Fonts and communicates with Google servers. By continuing to use our website, you agree to the use of cookies and our privacy policy.